[ad_1]
Aurich Lawson | Getty Pictures
Beforehand, on “Weekend Tasks for Homelab Admins With Management Points,” we created our personal dynamically updating DNS and DHCP setup with bind and dhcpd. We laughed. We cried. We hurled. Bonds have been cast, by no means to be damaged. And I hope all of us took somewhat one thing particular away from the journey—particularly, a dynamically updating DNS and DHCP setup. Which we’re now going to place to make use of!
If you happen to’re becoming a member of us contemporary, with out having gone by the earlier half and eager to comply with this tutorial, howdy! There may be some elements which can be tougher to finish with out a native occasion of bind (or different authoritative resolver appropriate with nsupdate). We’ll speak extra about this after we get there, however simply know that if you wish to pause and go do part one first, you could have a better time following alongside.
The short model: A LetsEncrypt of our personal
This text will stroll by the method of putting in step-ca, a standalone certificates authority-in-a-box. We’ll then configure step-ca with an ACME provisioner—that is Automatic Certificate Management Environment, the expertise that underpins LetsEncrypt and facilitates the automated provisioning, renewal, and revocation of SSL/TLS certificates.
After we get step-ca listening for incoming ACME requests, we’ll speak by the methods to get the self-hosted providers in your LAN-speaking ACME to allow them to begin robotically requesting certificates from our step-ca certificates authority—similar to how LetsEncrypt works.
I will focus solely on utilizing acme.sh for requesting and renewing certs on shoppers as a result of it is the instrument I am most acquainted with. However all the things we do ought to be doable with any ACME consumer, so for those who’re extra comfortable with certbot or dehydrated no matter, be happy to make use of that in your shoppers. The directions ought to be fairly straightforward to adapt.
I didn’t perceive any of that—we’re doing what now?
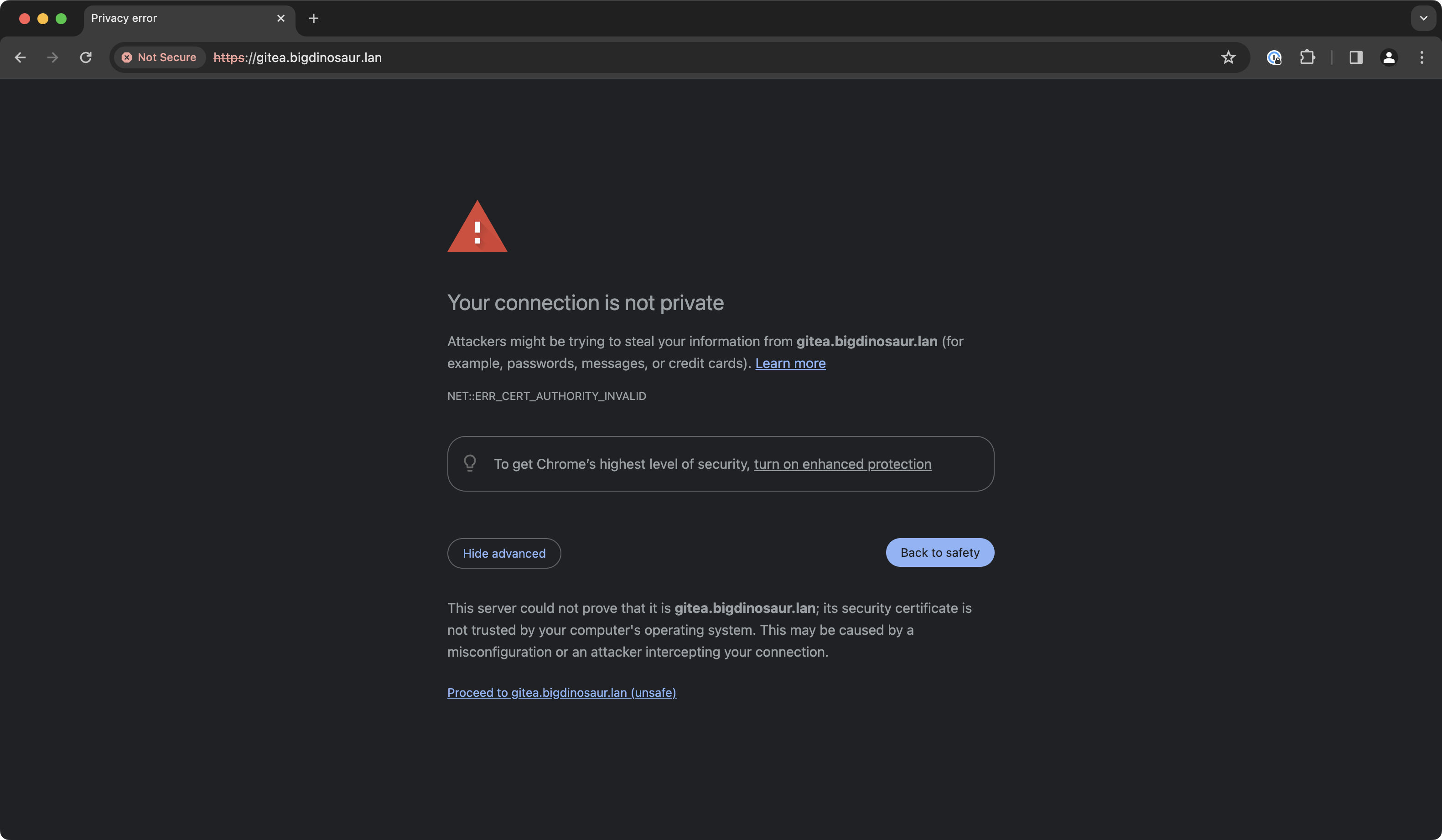
So you understand how you put in a brand new self-hosted factor in your LAN, and once you log into its net interface, you get a “your connection is not safe” warning as a result of the factor you simply put in is utilizing a self-signed TLS certificates?
Lee Hutchinson
These warnings appear spurious, and most of the people rapidly change into blind to them, however they serve a vital function—even when it is a function lots of people do not care about.
See, net browsers use TLS and HTTPS to attempt to accomplish two linked and equally necessary issues: first, and most clearly, to encrypt the connection between you and the net useful resource you are accessing. However the second function—the one upended by self-signed certs and the supply of the large warnings—is id verification. An assurance that your encrypted communication goes to the particular person you assume it is going to is sort of as very important as having the communication encrypted within the first place.
A sequence of belief extends from the assorted root certificate authorities down by the TLS certificates they subject to endpoints, and, at the very least in idea, one ought to have the ability to belief {that a} CA has finished some quantity of due diligence to confirm the id and possession of the endpoints it points certificates to. While you belief a certificates authority, you’re trusting that the id attestations on the certificates that CA points are in actual fact correct—that seeing a cert for “www.instance.com” actually does imply you are searching “www.instance.com” and never a website pretending to be that (or that your connection is not being compromised through a man-in-the-middle sort assault).
Self-signed certificates break that chain of belief. Your browser has no strategy to validate that the useful resource is what its certificates says it’s, as a result of your browser does not belief the issuer.
That is why browsers present massive scary warnings once you go to a web page that presents a self-signed cert: You could have encryption, however no id verification. To banish the warnings, we’ve got to have each—which is what we purpose to offer with our step-ca set up. We will arrange our personal CA and get it trusted by your browser and by the gadgets and providers for which it is going to be issuing certificates.
[ad_2]
Source link








