[ad_1]
Getty Photos
Ars Technica was just lately used to serve second-stage malware in a marketing campaign that used a never-before-seen assault chain to cleverly cowl its tracks, researchers from safety agency Mandiant reported Tuesday.
A benign picture of a pizza was uploaded to a third-party web site and was then linked with a URL pasted into the “about” web page of a registered Ars person. Buried in that URL was a string of characters that seemed to be random—however had been truly a payload. The marketing campaign additionally focused the video-sharing web site Vimeo, the place a benign video was uploaded and a malicious string was included within the video description. The string was generated utilizing a way often known as Base 64 encoding. Base 64 converts textual content right into a printable ASCII string format to characterize binary information. Gadgets already contaminated with the first-stage malware used within the marketing campaign routinely retrieved these strings and put in the second stage.
Not sometimes seen
“This can be a totally different and novel manner we’re seeing abuse that may be fairly exhausting to detect,” Mandiant researcher Yash Gupta mentioned in an interview. “That is one thing in malware we have now not sometimes seen. It’s fairly fascinating for us and one thing we wished to name out.”
The picture posted on Ars appeared within the about profile of a person who created an account on November 23. An Ars consultant mentioned the picture, displaying a pizza and captioned “I really like pizza,” was eliminated by Ars employees on December 16 after being tipped off by e mail from an unknown get together. The Ars profile used an embedded URL that pointed to the picture, which was routinely populated into the about web page. The malicious base 64 encoding appeared instantly following the professional a part of the URL. The string didn’t generate any errors or forestall the web page from loading.
Mandiant researchers said there have been no penalties for individuals who could have considered the picture, both as displayed on the Ars web page or on the web site that hosted it. It’s additionally not clear that any Ars customers visited the about web page.
Gadgets that had been contaminated by the primary stage routinely accessed the malicious string on the finish of the URL. From there, they had been contaminated with a second stage.
The video on Vimeo labored equally, besides that the string was included within the video description.
Ars representatives had nothing additional so as to add. Vimeo representatives didn’t instantly reply to an e mail.
The marketing campaign got here from a risk actor Mandiant tracks as UNC4990, which has been energetic since at the least 2020 and bears the hallmarks of being motivated by monetary achieve. The group has already used a separate novel approach to fly below the radar. That approach unfold the second stage utilizing a textual content file that browsers and regular textual content editors confirmed to be clean.
Opening the identical file in a hex editor—a software for analyzing and forensically investigating binary recordsdata—confirmed {that a} mixture of tabs, areas, and new traces had been organized in a manner that encoded executable code. Just like the approach involving Ars and Vimeo, the usage of such a file is one thing the Mandiant researchers had by no means seen earlier than. Beforehand, UNC4990 used Github and Gitlab.
The preliminary stage of the malware was transmitted by contaminated USB drives. The drives put in a payload Mandiant has dubbed explorerps1. Contaminated gadgets then routinely reached out to both the malicious textual content file or else to the URL posted on Ars or the video posted to Vimeo. The bottom 64 strings within the picture URL or video description, in flip, prompted the malware to contact a web site internet hosting the second stage. The second stage of the malware, tracked as Emptyspace, constantly polled a command-and-control server that, when instructed, would obtain and execute a 3rd stage.
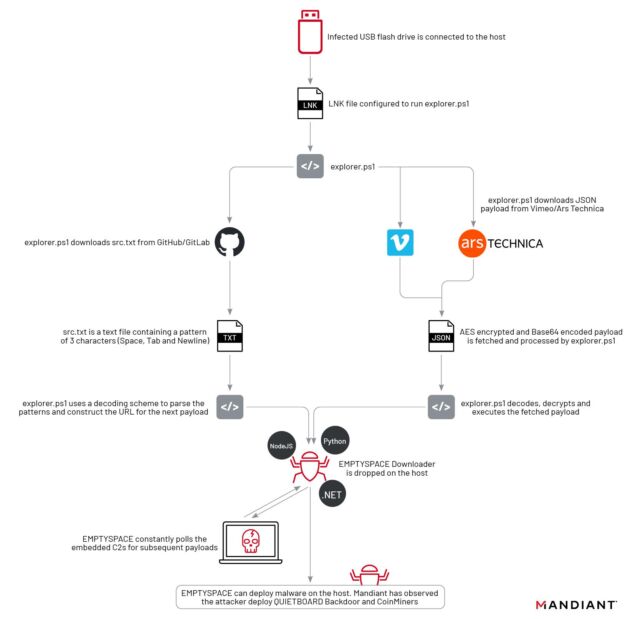
Mandiant
Mandiant has noticed the set up of this third stage in just one case. This malware acts as a backdoor the researchers monitor as Quietboard. The backdoor in that case went on to put in a cryptocurrency miner.
Anybody who is worried they might have been contaminated by any of the malware coated by Mandiant can examine the indications of compromise part in Tuesday’s submit.
[ad_2]
Source link








