[ad_1]
Unknown menace actors are actively focusing on two crucial zero-day vulnerabilities that enable them to bypass two-factor authentication and execute malicious code inside networks that use a extensively used digital non-public community equipment offered by Ivanti, researchers mentioned Wednesday.
Ivanti reported bare-bones particulars in regards to the zero-days in posts revealed on Wednesday that urged clients to comply with mitigation steerage instantly. Tracked as CVE-2023-846805 and CVE-2024-21887, they reside in Ivanti Join Safe, a VPN equipment typically abbreviated as ICS. Previously often known as Pulse Safe, the extensively used VPN has harbored previous zero-days in recent years that got here beneath widespread exploitation, in some instances to devastating impact.
Exploiters: Begin your engines
“When mixed, these two vulnerabilities make it trivial for attackers to run instructions on the system,” researchers from safety agency Volexity wrote in a post summarizing their investigative findings of an assault that hit a buyer final month. “On this specific incident, the attacker leveraged these exploits to steal configuration knowledge, modify present recordsdata, obtain distant recordsdata, and reverse tunnel from the ICS VPN equipment.” Researchers Matthew Meltzer, Robert Jan Mora, Sean Koessel, Steven Adair, and Thomas Lancaster went on to jot down:
Volexity noticed the attacker modifying reliable ICS elements and making adjustments to the system to evade the ICS Integrity Checker Instrument. Notably, Volexity noticed the attacker backdooring a reliable CGI file (compcheck.cgi) on the ICS VPN equipment to permit command execution. Additional, the attacker additionally modified a JavaScript file utilized by the Internet SSL VPN element of the gadget so as to keylog and exfiltrate credentials for customers logging into it. The data and credentials collected by the attacker allowed them to pivot to a handful of methods internally, and finally acquire unfettered entry to methods on the community.
The researchers attributed the hacks to a menace actor tracked beneath the alias UTA0178, which they think is a Chinese language nation-state-level menace actor.
Like different VPNs, the ICS sits on the fringe of a protected community and acts because the gatekeeper that’s supposed to permit solely approved units to attach remotely. That place and its always-on standing make the equipment perfect for focusing on when code-execution vulnerabilities in them are recognized. To date, the zero-days seem to have been exploited in low numbers and solely in extremely focused assaults, Volexity CEO Steven Adair mentioned in an e-mail. He went on to jot down:
Nevertheless, there’s a superb likelihood that would change. There’ll now be a possible race to compromise units earlier than mitigations are utilized. It is usually potential that the menace actor might share the exploit or that further attackers will in any other case determine the exploit. If you realize the main points—the exploit is kind of trivial to drag off and it requires completely no authentication and might be achieved over the Web. Your entire functions of those units are to offer VPN entry, so by nature they sit on the Web and are accessible.
The menace panorama of 2023 was dominated by the energetic mass exploitation of a handful of high-impact vulnerabilities tracked beneath the names Citrix Bleed or designations together with CVE-2023-36934, CVE-2022-47966, and CVE-2023-49103, which resided within the Citrix NetScaler Utility Supply Controller and NetScaler Gateway, MOVEit from maker Progress Software program, 24 wares offered by Zoho-owned ManageEngine and ownCloud, respectively. Except affected organizations transfer extra rapidly than they did final 12 months to patch their networks, the most recent vulnerabilities within the Ivanti home equipment might obtain the identical therapy.
Researcher Kevin Beaumont, who proposed “Join Round” as a moniker for monitoring the zero-days, posted results from a scan that confirmed there have been roughly 15,000 affected Ivanti home equipment around the globe uncovered to the Web. Beaumont mentioned that hackers backed by a nation-state seemed to be behind the assaults on the Ivanti-sold gadget.
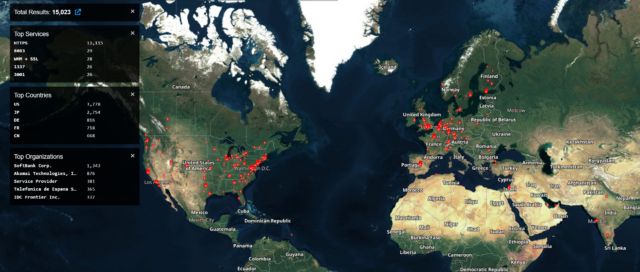
Shodan
[ad_2]
Source link








