[ad_1]
Getty Photographs
Orange España, Spain’s second-biggest cell operator, suffered a serious outage on Wednesday after an unknown get together obtained a “ridiculously weak” password and used it to entry an account for managing the worldwide routing desk that controls which networks ship the corporate’s Web site visitors, researchers stated.
The hijacking started round 9:28 Coordinated Common Time (about 2:28 Pacific time) when the get together logged into Orange’s RIPE NCC account utilizing the password “ripeadmin” (minus the citation marks). The RIPE Community Coordination Middle is certainly one of 5 Regional Internet Registries, that are liable for managing and allocating IP addresses to Web service suppliers, telecommunication organizations, and firms that handle their very own community infrastructure. RIPE serves 75 international locations in Europe, the Center East, and Central Asia.
“Issues obtained ugly”
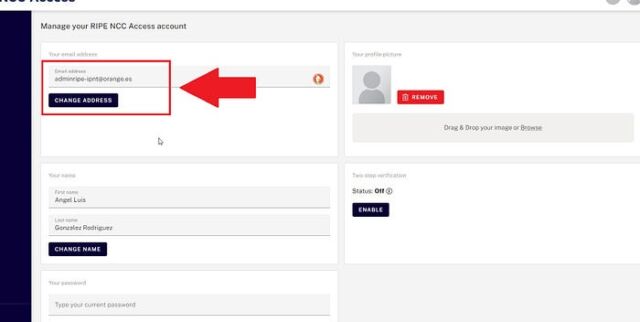
The password got here to mild after the get together, utilizing the moniker Snow, posted a picture to social media that confirmed the orange.es e-mail deal with related to the RIPE account. RIPE stated it is engaged on methods to beef up account safety.
Safety agency Hudson Rock plugged the e-mail deal with right into a database it maintains to trace credentials on the market in on-line bazaars. In a post, the safety agency stated the username and “ridiculously weak” password have been harvested by information-stealing malware that had been put in on an Orange pc since September. The password was then made out there on the market on an infostealer market.
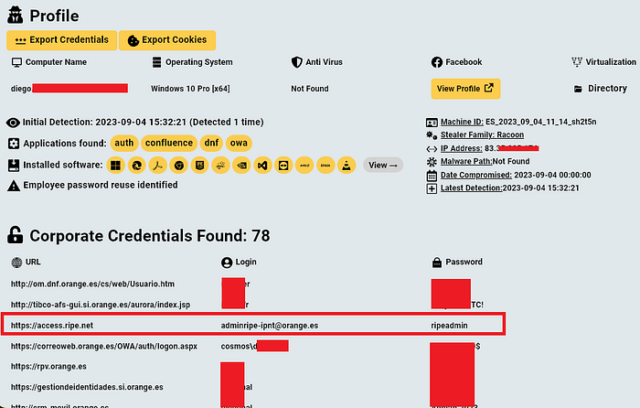
HJudson Rock
Researcher Kevin Beaumont said hundreds of credentials defending different RIPE accounts are additionally out there in such marketplaces.
As soon as logged into Orange’s RIPE account, Snow made modifications to the worldwide routing desk the cell operator depends on to specify what spine suppliers are licensed to hold its site visitors to varied elements of the world. These tables are managed utilizing the Border Gateway Protocol (BGP), which connects one regional community to the remainder of the Web. Particularly, Snow added a number of new ROAs, brief for Route Origin Authorizations. These entries enable “autonomous methods” equivalent to Orange’s AS12479 to designate different autonomous methods or giant chunks of IP addresses to ship its site visitors to varied areas of the world.
Within the preliminary stage, the modifications had no significant impact as a result of the ROAs Snow added asserting the IP addresses—93.117.88.0/22 and 93.117.88.0/21, and 149.74.0.0/16—already originated with Orange’s AS12479. A couple of minutes later, Snow added ROAs to 5 extra routes. All however certainly one of them additionally originated with the Orange AS, and as soon as once more had no impact on site visitors, in line with a detailed writeup of the occasion by Doug Madory, a BGP skilled at safety and networking agency Kentik.
The creation of the ROA for 149.74.172.0/22 was the primary act by Snow to create issues, as a result of it contained a subset of IP addresses within the beforehand introduced 149.74.0.0/16 block.
“It invalidated any routes which might be extra particular (longer prefix size) than a 16,” Madory informed Ars in an internet interview. “So routes like 149.74.100.0/23 grew to become invalid and began getting filtered. Then [Snow] created extra ROAs to cowl these routes. Why? Undecided. I believe, at first, they have been simply messing round. Earlier than that ROA was created, there was no ROA to say something about this deal with vary.”
[ad_2]
Source link








