[ad_1]
Miscreants are actively exploiting two new zero-day vulnerabilities to wrangle routers and video recorders right into a hostile botnet utilized in distributed denial-of-service assaults, researchers from networking agency Akamai stated Thursday.
Each of the vulnerabilities, which have been beforehand unknown to their producers and to the safety analysis neighborhood at giant, permit for the distant execution of malicious code when the affected units use default administrative credentials, in response to an Akamai post. Unknown attackers have been exploiting the zero-days to compromise the units to allow them to be contaminated with Mirai, a potent piece of open supply software program that makes routers, cameras, and different kinds of Web of Issues units a part of a botnet that’s able to waging DDoSes of beforehand unimaginable sizes.
Akamai researchers stated one of many zero-days underneath assault resides in a number of fashions of community video recorders. The opposite zero-day resides in an “outlet-based wi-fi LAN router constructed for lodges and residential functions.” The router is bought by a Japan-based producer, which “produces a number of switches and routers.” The router characteristic being exploited is “a quite common one,” and the researchers can’t rule out the likelihood it’s being exploited in a number of router fashions bought by the producer.
Akamai stated it has reported the vulnerabilities to each producers, and that one in every of them has offered assurances safety patches will probably be launched subsequent month. Akamai stated it wasn’t figuring out the precise units or the producers till fixes are in place to stop the zero-days from being extra extensively exploited.
“Though this data is proscribed, we felt it was our accountability to alert the neighborhood concerning the ongoing exploitation of those CVEs within the wild. There’s a skinny line between accountable disclosing data to assist defenders, and oversharing data that may allow additional abuse by hordes of risk actors.”
The Akamai submit supplies a bunch of file hashes and IP and area addresses getting used within the assaults. House owners of community video cameras and routers can use this data to see if units on their networks have been focused.
The distant code execution makes use of a way referred to as command injection, which first requires an attacker to authenticate itself utilizing the credentials configured within the susceptible gadget. The authentication and injection is carried out utilizing an ordinary POST request.
In an e mail, Akamai researcher Larry Cashdollar wrote:
The units do not sometimes permit code execution by means of the administration interface. For this reason getting RCE by means of command injection is required.
As a result of the attacker must authenticate first they should know some login credentials that may work. If the units are utilizing straightforward guessable logins like admin:password or admin:password1 these could possibly be in danger too if somebody expands the record of credentials to attempt.
He stated that each producers have been notified, however solely one in every of them has thus far dedicated to releasing a patch, which is anticipated subsequent month. The standing of a repair from the second producer is at present unknown.
Cashdollar stated an incomplete Web scan confirmed there are a minimum of 7,000 susceptible units. The precise variety of affected units could also be greater.
Mirai first got here to widespread public consideration in 2016, when a botnet—that means a community of compromised units underneath the management of a hostile risk actor—took down the safety information website KrebsOnSecurity with what was then a record-setting 620 gigabit-per-second DDoS.
Moreover its huge firepower, Mirai stood out for different causes. For one, the units it commandeers have been an ensemble of routers, safety cameras and different kinds of IoT units, one thing that had been largely unseen previous to that. And for one more, the underlying supply code shortly became freely available. Quickly, Mirai was being utilized in even bigger DDoSes concentrating on gaming platforms and the ISPs that serviced them. Mirai and different IoT botnets have been a reality of Web life ever since.
The Mirai pressure used within the assaults found by Akamai is primarily an older one referred to as JenX. It has been modified, nevertheless, to make use of many fewer domains than normal to hook up with command-and-control servers. Some malware samples additionally present ties to a separate Mirai variant referred to as hailBot.
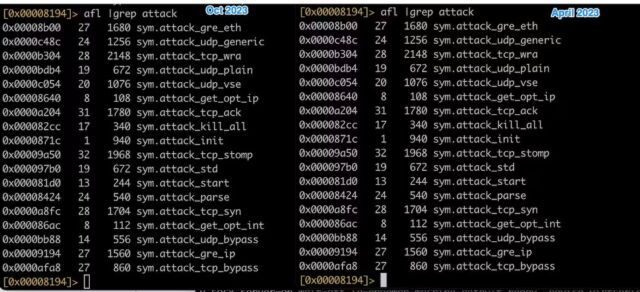
The code used within the zero-day assaults noticed by Akamail—together with offensive racist slurs—are nearly similar to that utilized in DDoS assaults a China-based safety agency noticed concentrating on a Russian information web site in Might. The picture under exhibits a side-by-side comparability.
Payloads exploiting the zero-days are:
alert tcp any any -> any any (msg:"InfectedSlurs 0day exploit #1 try"; content material:"lang="; content material:"useNTPServer="; content material:"synccheck="; content material:"timeserver="; content material:"interval="; content material:"enableNTPServer="; sid:1000006;)
and
alert tcp any any -> any any (msg:"InfectedSlurs 0day exploit #2 try"; content material:"page_suc="; content material:"system.normal.datetime="; content material:"ntp.normal.hostname="; pcre:"ntp.normal.hostname="; content material:"ntp.normal.dst="; content material:"ntp.normal.dst.alter="; content material:"system.normal.timezone="; content material:"system.normal.tzname="; content material:"ntp.normal.allow="; sid:1000005;)
Individuals or organizations involved with the likelihood they’re being focused with these exploits can use Snort rules and indicators of compromise printed by Akamail to detect and repel assaults. In the meanwhile, there isn’t any method to determine the precise units which might be susceptible or the producers of these units.
[ad_2]
Source link








