[ad_1]
GPUs from all six of the most important suppliers are weak to a newly found assault that permits malicious web sites to learn the usernames, passwords, and different delicate visible information displayed by different web sites, researchers have demonstrated in a paper printed Tuesday.
The cross-origin assault permits a malicious web site from one area—say, instance.com—to successfully learn the pixels displayed by an internet site from instance.org, or one other totally different area. Attackers can then reconstruct them in a manner that permits them to view the phrases or pictures displayed by the latter web site. This leakage violates a vital safety precept that varieties one of the crucial elementary safety boundaries safeguarding the Web. Referred to as the same origin policy, it mandates that content material hosted on one web site area be remoted from all different web site domains.
Optimizing bandwidth at a value
GPU.zip, because the proof-of-concept assault has been named, begins with a malicious web site that locations a hyperlink to the webpage it needs to learn inside an iframe, a standard HTML ingredient that permits websites to embed advertisements, pictures, or different content material hosted on different web sites. Usually, the identical origin coverage prevents both web site from inspecting the supply code, content material, or remaining visible product of the opposite. The researchers discovered that information compression that each inside and discrete GPUs use to enhance efficiency acts as a side channel that they’ll abuse to bypass the restriction and steal pixels one after the other.
“We discovered that fashionable GPUs robotically attempt to compress this visible information, with none software involvement,” Yingchen Wang, the lead writer and a researcher on the College of Texas at Austin, wrote in an e mail. “That is executed to avoid wasting reminiscence bandwidth and enhance efficiency. Since compressibility is information dependent, this optimization creates a aspect channel which could be exploited by an attacker to disclose details about the visible information.”
For GPU.zip to work, a malicious web page should be loaded into the Chrome or Edge browsers. Beneath-the-hood variations in the way in which Firefox and Safari work forestall the assault from succeeding when these browsers course of an assault web page. One other requirement is that the web page linked to within the iframe should not be configured to disclaim being embedded by cross-origin web sites.
The safety threats that may outcome when HTML is embedded in iframes on malicious web sites have been well-known for greater than a decade. Most web sites restrict the cross-origin embedding of pages displaying consumer names, passwords, or different delicate content material via X-Body-Choices or Content material-Safety-Coverage headers. Not all, nonetheless, do. One instance is Wikipedia, which exhibits the usernames of people that log in to their accounts. An individual who needs to stay nameless whereas visiting a web site they don’t belief could possibly be outed if it contained an iframe containing a hyperlink to https://en.wikipedia.org/wiki/Main_Page.
Wang et al.
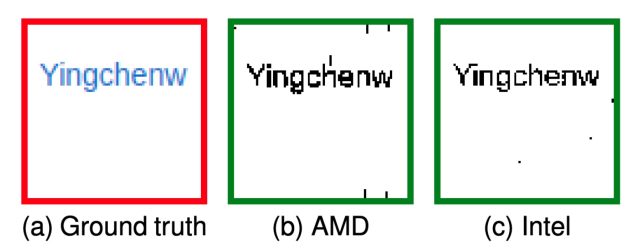
The researchers confirmed how GPU.zip permits a malicious web site they created for his or her PoC to steal pixels one after the other for a consumer’s Wikipedia username. The assault works on GPUs offered by Apple, Intel, AMD, Qualcomm, Arm, and Nvidia. On AMD’s Ryzen 7 4800U, GPU.zip took about half-hour to render the focused pixels with 97 p.c accuracy. The assault required 215 minutes to reconstruct the pixels when displayed on a system operating an Intel i7-8700.
The entire GPUs analyzed use proprietary types of compression to optimize the bandwidth accessible within the reminiscence information bus of the PC, telephone, or different system displaying the focused content material. The compression schemes differ from producer to producer and are undocumented, so the researchers reverse-engineered every one. The insights yielded a way that makes use of the SVG, or the scalable vector graphics picture format, to maximise variations in DRAM visitors between black and white goal pixels within the presence of compression. Whereas their paper discusses GPU.zip because it applies to iGPUs, or inside GPUs, the method applies equally to standalone or discrete GPUs as nicely.
Of their paper, the researchers wrote:
We display that an attacker can exploit the iGPU-based compression channel to carry out cross-origin pixel stealing assaults within the browser utilizing SVG filters (the newest model of Google Chrome as of April 2023), although SVG filters are applied at fixed time. The reason being that the attacker can create extremely redundant or extremely non-redundant patterns relying on a single secret pixel within the browser. As these patterns are processed by the iGPU, their various levels of redundancy trigger the lossless compression output to depend upon the key pixel. The info-dependent compression output immediately interprets to data-dependent DRAM visitors and data-dependent cache occupancy. Consequently, we present that, even below probably the most passive risk mannequin—the place an attacker can solely observe coarse-grained redundancy data of a sample utilizing a coarse-grained timer within the browser and lacks the power to adaptively choose enter—particular person pixels could be leaked. Our proof-of-concept assault succeeds on a spread of gadgets (together with computer systems, telephones) from quite a lot of {hardware} distributors with distinct GPU architectures (Intel, AMD, Apple, Nvidia). Surprisingly, our assault additionally succeeds on discrete GPUs, and we’ve got preliminary outcomes indicating the presence of software-transparent compression on these architectures as nicely.
[ad_2]
Source link







