[ad_1]
Aurich Lawson | Getty Pictures
Researchers on Wednesday introduced a serious cybersecurity discover—the world’s first-known occasion of real-world malware that may hijack a pc’s boot course of even when Safe Boot and different superior protections are enabled and operating on absolutely up to date variations of Home windows.
Dubbed BlackLotus, the malware is what’s often called a UEFI bootkit. These subtle items of malware infect the UEFI—brief for Unified Extensible Firmware Interface—the low-level and complicated chain of firmware answerable for booting up nearly each trendy laptop. Because the mechanism that bridges a PC’s machine firmware with its working system, the UEFI is an OS in its personal proper. It’s positioned in an SPI-connected flash storage chip soldered onto the pc motherboard, making it tough to examine or patch.
As a result of the UEFI is the very first thing to run when a pc is turned on, it influences the OS, safety apps, and all different software program that follows. These traits make the UEFI the proper place to run malware. When profitable, UEFI bootkits disable OS safety mechanisms and make sure that a pc stays contaminated with stealthy malware that runs on the kernel mode or person mode, even after the working system is reinstalled or a tough drive is changed.
As interesting as it’s to risk actors to put in almost invisible and unremovable malware that has kernel-level entry, there are a couple of formidable hurdles standing of their approach. One is the requirement that they first hack the machine and achieve administrator system rights, both by exploiting a number of vulnerabilities within the OS or apps or by tricking a person into putting in trojanized software program. Solely after this excessive bar is cleared can the risk actor try an set up of the bootkit.
The second factor standing in the best way of UEFI assaults is UEFI Secure Boot, an industry-wide commonplace that makes use of cryptographic signatures to make sure that each bit of software program used throughout startup is trusted by a pc’s producer. Safe Boot is designed to create a series of belief that can stop attackers from changing the meant bootup firmware with malicious firmware. If a single firmware hyperlink in that chain isn’t acknowledged, Safe Boot will stop the machine from beginning.
Whereas researchers have discovered Safe Boot vulnerabilities up to now, there was no indication that risk actors have ever been in a position to bypass the safety within the 12 years it has been in existence. Till now.
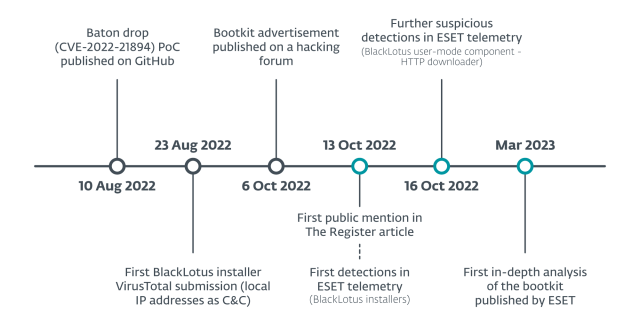
On Wednesday, researchers at safety agency ESET introduced a deep-dive analysis of the world’s first in-the-wild UEFI bootkit that bypasses Safe Boot on absolutely up to date UEFI techniques operating absolutely up to date variations of Home windows 10 and 11. Whereas there are not any strings or different indicators immediately displaying the title of the creators or the bootkit, ESET researchers have concluded that it virtually actually corresponds to a bootkit, often called BlackLotus, that has been advertised in underground cybercrime boards since final 12 months. The worth: $5,000, and $200 thereafter for updates.
ESET
To defeat Safe Boot, the bootkit exploits CVE-2022-21894, a vulnerability in all supported variations of Home windows that Microsoft patched in January 2022. The reminiscence corruption flaw, known as Baton Drop by the researcher who found it, will be exploited to take away Safe Boot capabilities from the boot sequence throughout startup. Attackers may also abuse the flaw to acquire keys for BitLocker, a Home windows characteristic for encrypting onerous drives.
CVE-2022-21894 has confirmed to be particularly priceless to the BlackLotus creators. Regardless of Microsoft releasing new patched software program, the weak signed binaries have but to be added to the UEFI revocation list that flags boot information that ought to now not be trusted. Microsoft has not defined the explanation, but it surely seemingly has to do with lots of of weak bootloaders that stay in use at the moment. If these signed binaries are revoked, thousands and thousands of units will now not work. Because of this, absolutely up to date units stay weak as a result of attackers can merely change patched software program with the older, weak software program.
[ad_2]
Source link








