[ad_1]
Researchers have found a intelligent piece of malware that stealthily exfiltrates information and executes malicious code from Home windows techniques by abusing a function in Microsoft Web Info Providers (IIS).
IIS is a general-purpose net server that runs on Home windows units. As an online server, it accepts requests from distant purchasers and returns the suitable response. In July 2021, community intelligence firm Netcraft said there have been 51.6 million situations of IIS unfold throughout 13.5 million distinctive domains.
IIS provides a function referred to as Failed Request Occasion Buffering that collects metrics and different information about net requests acquired from distant purchasers. Shopper IP addresses and port and HTTP headers with cookies are two examples of the information that may be collected. FREB helps directors troubleshoot failed net requests by retrieving ones assembly sure standards from a buffer and writing them to disk. The mechanism can assist decide the reason for 401 or 404 errors or isolate the reason for stalled or aborted requests.
Legal hackers have discovered the best way to abuse this FREB function to smuggle and execute malicious code into protected areas of an already compromised community. The hackers may use FREB to exfiltrate information from the identical protected areas. As a result of the method blends in with reputable eeb requests, it offers a stealthy solution to additional burrow into the compromised community.
The post-exploit malware that makes this attainable has been dubbed Frebniis by researchers from Symantec, who reported on its use on Thursday. Frebniis first ensures FREB is enabled after which hijacks its execution by injecting malicious code into the IIS course of reminiscence and inflicting it to run. As soon as the code is in place, Frebniis can examine all HTTP requests acquired by the IIS server.
“By hijacking and modifying IIS net server code, Frebniis is ready to intercept the common move of HTTP request dealing with and search for specifically formatted HTTP requests,” Symantec researchers wrote. “These requests enable distant code execution and proxying to inner techniques in a stealthy method. No information or suspicious processes might be operating on the system, making Frebniis a comparatively distinctive and uncommon sort of HTTP backdoor seen within the wild.”
Earlier than Frebniis can work, an attacker should first hack the Home windows system operating the IIS server. Symantec researchers have but to find out how Frebniis does this.
Frebniis parses all HTTP POST requests invoking the logon.aspx or default.aspx information, that are used to create login pages and serve default net pages, respectively. Attackers can smuggle requests into an contaminated server by sending one in every of these requests and including the password “7ux4398!” as a parameter. As soon as such a request is acquired, Frebniis decrypts and executes .Internet code that controls the primary backdoor capabilities. To make the method extra stealthy, the code drops no information to disk.
The .NET code serves two functions. First, it offers a proxy that permits attackers to make use of the compromised IIS server to work together or talk with inner sources that will in any other case be inaccessible from the Web. The next desk exhibits the instructions it’s programmed to hold out:
| Command | Operate identify | Parameter | Description |
|---|---|---|---|
| 1 | CreateConnect | Host:Port | Hook up with a distant system for proxying, returns a UUID representing the distant system |
| 2 | ReadScoket | Uuid | Learn a Base64 string from a distant system |
| 3 | Writescoket | Uuid, Base64 string | Write a Base64 string to a distant system |
| 4 | CloseScoket | Uuid | Shut the connection |
The second function of the .Internet code is to permit the distant execution of attacker-provided code on the IIS server. By sending a request to the logon.aspx or default.aspx information that features code written in C#, Frebniis will mechanically decode it and execute it in reminiscence. As soon as once more, by executing the code straight in reminiscence, the backdoor is way tougher to detect.
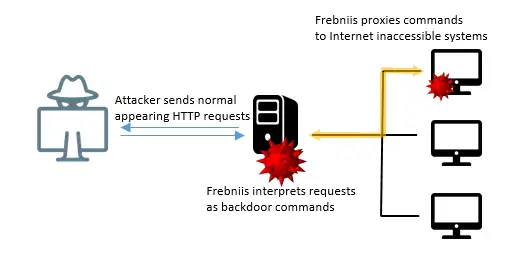
Diagram displaying how Frebniis is used.
Symantec
It’s not clear how extensively used Frebniis is in the mean time. The submit offers two file hashes related to the backdoor however doesn’t clarify the best way to search a system to see in the event that they exist.
[ad_2]
Source link








