[ad_1]
Researchers have uncovered a malicious Android app that may tamper with the wi-fi router the contaminated cellphone is linked to and pressure the router to ship all community units to malicious websites.
The malicious app, found by Kaspersky, makes use of a way often known as DNS (Area Title System) hijacking. As soon as the app is put in, it connects to the router and makes an attempt to log in to its administrative account through the use of default or generally used credentials, corresponding to admin:admin. When profitable, the app then modifications the DNS server to a malicious one managed by the attackers. From then on, units on the community could be directed to imposter websites that mimic reputable ones however unfold malware or log person credentials or different delicate info.
Able to spreading extensively
“We imagine that the invention of this new DNS changer implementation is essential when it comes to safety,” Kaspersky researchers wrote. “The attacker can use it to handle all communications from units utilizing a compromised Wi-Fi router with the rogue DNS settings.”
The researchers continued: “Customers join contaminated Android units to free/public Wi-Fi in such locations as cafes, bars, libraries, accommodations, procuring malls, and airports. When linked to a focused Wi-Fi mannequin with susceptible settings, the Android malware will compromise the router and have an effect on different units as effectively. Consequently, it’s able to spreading extensively within the focused areas.”
DNS is the mechanism that matches a website title like ArsTechnica.com to 18.188.231.255, the numerical IP handle the place the location is hosted. DNS lookups are carried out by servers operated by a person’s ISP or by companies from corporations corresponding to Cloudflare or Google. By altering the DNS server handle in a router’s administrative panel from a reputable one to a malicious one, attackers may cause all units linked to the router to obtain malicious area lookups that result in lookalike websites used for cybercrime.
The Android app is called Wroba.o, and has been in use for years in varied international locations, together with the US, France, Japan, Germany, Taiwan, and Turkey. Curiously, the DNS hijacking method the malware is able to is getting used virtually completely in South Korea. From 2019 to most of 2022, attackers lured targets to malicious websites that had been despatched by textual content messages, a way often known as smishing. Late final 12 months, the attackers included DNS hijacking into their actions in that Asian nation.
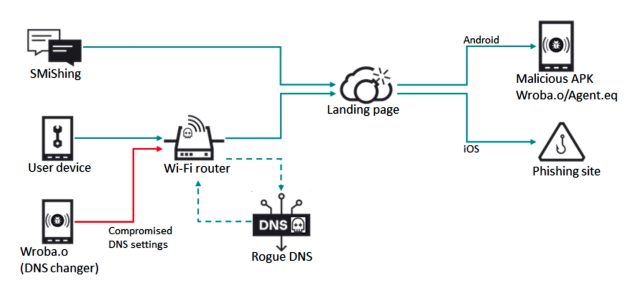
The attackers, recognized within the safety trade as Roaming Mantis, designed the DNS hijacking to work solely when units go to the cell model of a spoofed web site, most certainly to make sure the marketing campaign goes undetected.
Whereas the menace is severe, it has a significant shortcoming—HTTPS. Transport Layer Safety (TLS) certificates that function the underpinning for HTTPS bind a website title corresponding to ArsTechnica.com to a personal encryption key that’s recognized solely to the location operator. Individuals directed to a malicious website masquerading as Ars Technica utilizing a contemporary browser will obtain warnings that the connection isn’t safe or shall be requested to approve a self-signed certificates, a observe that customers ought to by no means observe.
One other technique to fight the menace is to make sure the password defending a router’s administrative account is modified from the default one to a powerful one.
Nonetheless, not everyone seems to be versed in such finest practices, which leaves them open to visiting a malicious website that appears virtually similar to the reputable one they meant to entry.
“Customers with contaminated Android units that hook up with free or public Wi-Fi networks might unfold the malware to different units on the community if the Wi-Fi community they’re linked to is susceptible,” Thursday’s report said. “Kaspersky specialists are involved in regards to the potential for the DNS changer for use to focus on different areas and trigger important points.
[ad_2]
Source link








