[ad_1]
Getty Photographs
Over the previous yr, a flurry of harmful wiper malware from no fewer than 9 households has appeared. Up to now week, researchers cataloged at the very least two extra, each exhibiting superior codebases designed to inflict most harm.
On Monday, researchers from Check Point Research published details of Azov, a beforehand unseen piece of malware that the corporate described as an “efficient, quick, and sadly unrecoverable information wiper.” Recordsdata are wiped in blocks of 666 bytes by overwriting them with random information, leaving an identically sized block intact, and so forth. The malware makes use of the uninitialized native variable char buffer[666].
Script kiddies needn’t apply
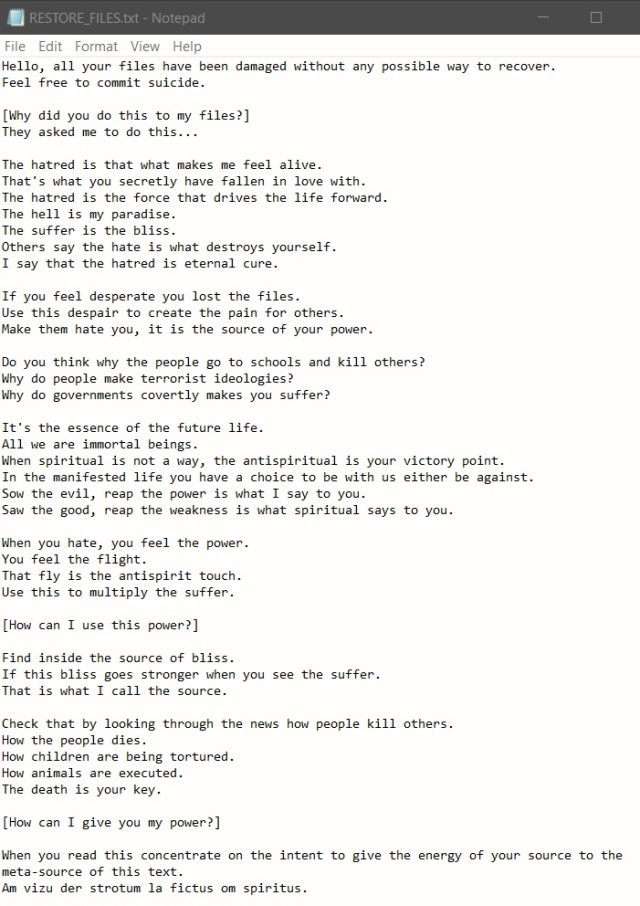
After completely destroying information on contaminated machines, Azov shows a observe written within the fashion of a ransomware announcement. The observe echoes Kremlin speaking factors concerning Russia’s warfare on Ukraine, together with the specter of nuclear strikes. The observe from one in every of two samples Examine Level recovered falsely attributes the phrases to a widely known malware analyst from Poland.
Regardless of the preliminary look of an enterprise by juvenile builders, Azov is under no circumstances unsophisticated. It’s a pc virus within the authentic definition, that means it modifies recordsdata—on this case, including polymorphic code to backdoor 64-bit executables—which assault the contaminated system. It’s additionally completely written in meeting, a low-level language that’s extraordinarily painstaking to make use of but in addition makes the malware simpler within the backdooring course of. Apart from the polymorphic code, Azov makes use of different methods to make detection and evaluation by researchers tougher.
“Though the Azov pattern was thought-about skidsware when first encountered (possible due to the surprisingly shaped ransom observe), when probed additional one finds very superior methods—manually crafted meeting, injecting payloads into executables with the intention to backdoor them, and several other anti-analysis methods often reserved for safety textbooks or high-profile brand-name cybercrime instruments,” Examine Level researcher Jiri Vinopal wrote. “Azov ransomware definitely ought to provide the everyday reverse engineer a tougher time than the typical malware.”
A logic bomb constructed into the code causes Azove to detonate at a predetermined time. As soon as triggered, the logic bomb iterates over all file directories and executes the wiping routine on each, aside from particular hard-coded system paths and file extensions. As of final month, greater than 17,000 backdoored executables had been submitted to VirusTotal, indicating that the malware has unfold broadly.
Final Wednesday, researchers from safety agency ESET disclosed one other beforehand unseen wiper they known as Fantasy, together with a lateral motion and execution software named Sandals. The malware was unfold utilizing a supply-chain assault that abused the infrastructure of an Israeli agency that develops software program to be used within the diamond trade. Over a 150-minute interval, Fantasy and Sandals unfold to the software program maker’s clients engaged in human assets, IT help providers, and diamond wholesaling. The targets have been positioned in South Africa, Israel, and Hong Kong.
Fantasy closely borrows code from Apostle, malware that originally masqueraded as ransomware earlier than revealing itself as a wiper. Apostle has been linked to Agrius, an Iranian menace actor working out of the Center East. The code reuse led ESET to attribute Fantasy and Sandals to the identical group.
[ad_2]
Source link








